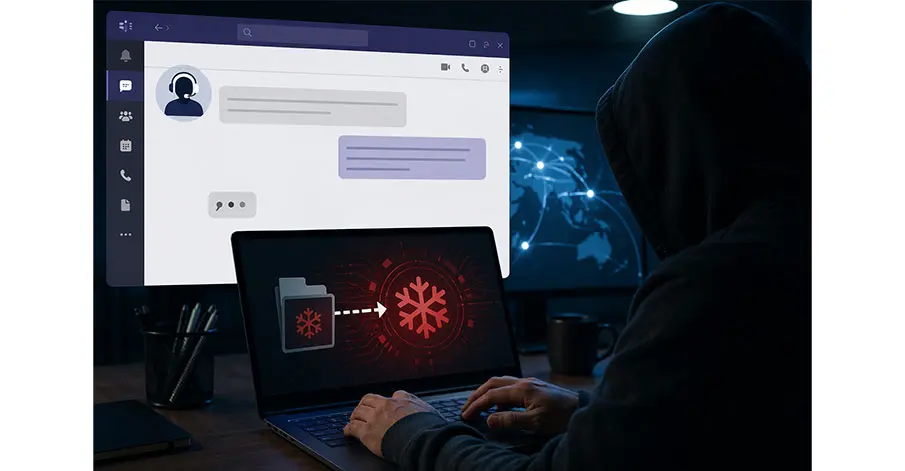
Cybersecurity researchers have uncovered a new wave of attacks in which hackers are exploiting Microsoft Teams to spread a dangerous malware toolkit known as “Snow”, raising fresh concerns over the misuse of workplace communication platforms.
Helpdesk Impersonation Tactics
According to security reports, a newly identified threat group, tracked as UNC6692, is targeting employees by posing as IT helpdesk staff. Attackers initiate contact via Teams chats, convincing victims to trust them and follow instructions.
Victims are often tricked into clicking malicious links or installing fake “patches,” which silently deploy the Snow malware onto their systems.
Targeting High-Level Employees
Researchers noted that the campaign disproportionately targets senior executives and key personnel, aiming to gain deeper access into corporate networks.
Once installed, the malware allows attackers to:
- Steal sensitive data
- Move laterally across systems
- Potentially deploy ransomware or conduct espionage
Blending Into Routine Activity
Experts warn that the attack is particularly dangerous because it mimics legitimate IT support interactions, making it difficult for users and even security systems to detect.
The use of trusted platforms like Teams further increases the success rate of such social engineering tactics.
Rising Threat to Organizations
Cybersecurity analysts say the campaign reflects a broader trend of attackers exploiting everyday workplace tools rather than traditional vulnerabilities.
Organizations are being urged to:
- Verify identities of IT staff before granting access
- Avoid clicking unsolicited links in chat platforms
- Strengthen employee cybersecurity awareness
- Implement strict access controls
A Growing Cyber Risk
The emergence of Snow malware highlights how cybercriminals are evolving their tactics, leveraging human trust and collaboration tools to bypass traditional defenses.
Experts caution that as remote work and digital collaboration expand, such threats are likely to become more frequent and sophisticated.