Cybersecurity researchers have uncovered the first known malicious Microsoft Outlook add-in discovered in the wild, in what experts describe as a significant expansion of supply chain attack risks targeting email users.
The phishing campaign, tracked as “AgreeToSteal,” exploited an abandoned Outlook calendar-scheduling add-in called AgreeTo to harvest credentials from more than 4,000 Microsoft accounts.
Originally launched in late 2022 as a legitimate productivity tool, AgreeTo was designed to help users consolidate calendar information and share availability. Although development of the add-in ceased and the developer’s domain later expired, the application reportedly remained available on the Microsoft Office Add-ins Store.
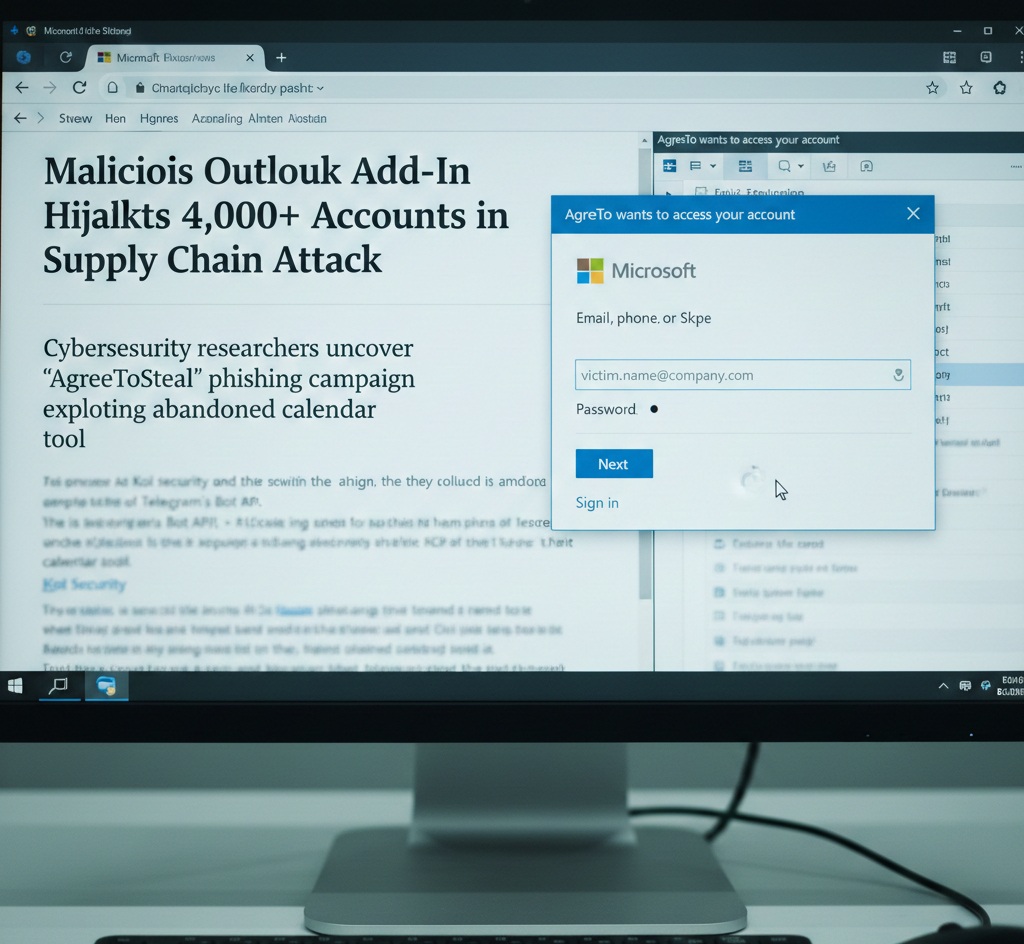
Fake Login Inside Outlook
According to researchers at Koi Security, when users opened the compromised add-in, they were presented not with a scheduling tool but with what appeared to be a legitimate Microsoft sign-in page embedded inside Outlook.
Once victims entered their email address and password, a simple JavaScript function captured the credentials along with the user’s IP address. The stolen data was then transmitted directly to attackers via Telegram’s Bot API, without the need for traditional command-and-control infrastructure.
After submission, users briefly saw a loading spinner before being redirected to the genuine Microsoft login page — leading many to believe they had simply been required to authenticate again. Unaware that their login details had already been compromised, victims continued using Outlook as normal.
Abuse of Trusted Add-In System
While technically simple, researchers said the attack’s effectiveness stemmed from its delivery method. The phishing interface operated within Outlook itself, was distributed through Microsoft’s official add-in platform, and appeared behind a trusted permission prompt.
Outlook add-ins function by loading web content through a developer-submitted XML manifest. Microsoft reviews and signs the manifest before listing it in the store. However, the actual content is pulled live from the developer’s server each time the add-in is opened — creating potential risks if that source becomes compromised or abandoned.
Because add-ins can operate with permissions such as “ReadWriteItem,” researchers warned that malicious actors could potentially do more than steal passwords, including reading, modifying or accessing sensitive mailbox data.
Security analysts say the incident highlights growing concerns around supply chain vulnerabilities and third-party integrations within widely used enterprise platforms.
Microsoft has not publicly commented on the specific case at the time of reporting.