Cybersecurity researchers have issued a fresh warning that the global boom in artificial intelligence is opening up a new and dangerous attack surface for Android users, after a sophisticated malware campaign was found exploiting the popularity of Hugging Face, one of the world’s largest AI and machine-learning platforms.
Security analysts say attackers are circulating a fake Android application, falsely branded as an official Hugging Face AI tool, which gives hackers near-total control over infected smartphones. The campaign highlights how growing interest in generative AI is being weaponised to deceive users who lack technical awareness of how AI platforms actually operate.
How the Fake App Spreads
The malicious application, appearing under names such as “HuggingFaceAI,” has been detected on third-party app stores, Telegram channels, and phishing pages shared via social media and messaging platforms.
Experts say the attackers are deliberately targeting users eager to experiment with AI tools. Unlike consumer-facing AI apps, Hugging Face does not offer an official standalone Android application, a gap cybercriminals are exploiting to appear legitimate.
What Happens After Installation
Once installed, the app silently deploys a powerful Android remote access trojan (RAT), effectively handing control of the device over to attackers. Researchers warn that compromised phones can be used to:
- Record the screen in real time
- Capture lock screen passwords
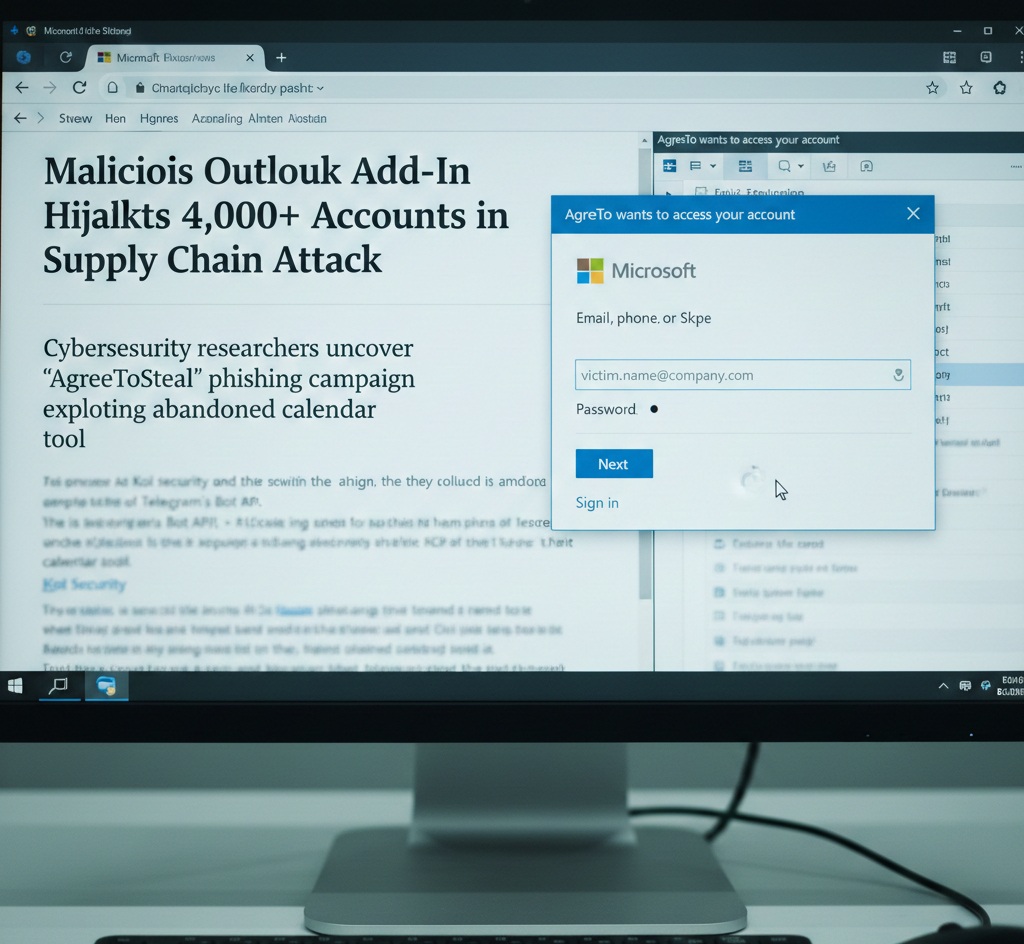
- Display fake login screens to steal credentials for apps such as Alipay and WeChat
“At that point, the phone effectively no longer belongs to its owner,” one analyst noted.
Why the Attack Is Hard to Detect
What makes the campaign particularly effective is its use of server-side polymorphism, a technique that continuously generates slightly altered versions of the malware to evade antivirus detection.
Researchers found that new malicious payloads were being created approximately every 15 minutes. During the investigation period, the repository hosting the malware was around 29 days old and had accumulated more than 6,000 commits, significantly complicating detection efforts.
Although Hugging Face employs tools such as ClamAV to scan uploaded files, security experts say the platform currently lacks strong filtering mechanisms to prevent large-scale abuse of its open repositories.
A Growing Trend in Android Malware
Mobile threat intelligence reports over the past year show that fake AI apps have become one of the most effective lures for Android malware. Experts say users are often tricked by alarming messages claiming their phone is infected and urging them to install a “free” AI-powered security or utility app.
Researchers across multiple cybersecurity firms have documented a sharp rise in trojans masquerading as AI chatbots, image generators, VPNs, and cryptocurrency tools. Some campaigns have reportedly infected tens of thousands of devices before being detected.
Android’s ability to sideload apps outside the Google Play Store continues to make it a prime target, particularly in regions where unofficial app marketplaces are widely used.
Risks for Users and Organisations
Compromised smartphones can be exploited for credential theft, financial fraud, surveillance, and even corporate espionage. In enterprise environments, infected personal devices may also serve as entry points into company networks under bring-your-own-device (BYOD) policies.
Hugging Face has since removed the malicious datasets after being alerted by security researchers, but experts warn that similar campaigns are likely to continue as AI platforms grow in influence.
Staying Safe
Cybersecurity professionals advise Android users to:
- Avoid installing apps from unofficial sources
- Be cautious of AI-branded apps promising “free” advanced features
- Verify developers before installation
- Keep devices updated with the latest security patches
As AI adoption accelerates globally — including in Pakistan — experts stress that digital awareness and platform-level safeguards must evolve just as rapidly to counter emerging cyber threats.